Make Architecture More Valuable: Take Ownership of Enterprise Process Automations and the Service Catalog
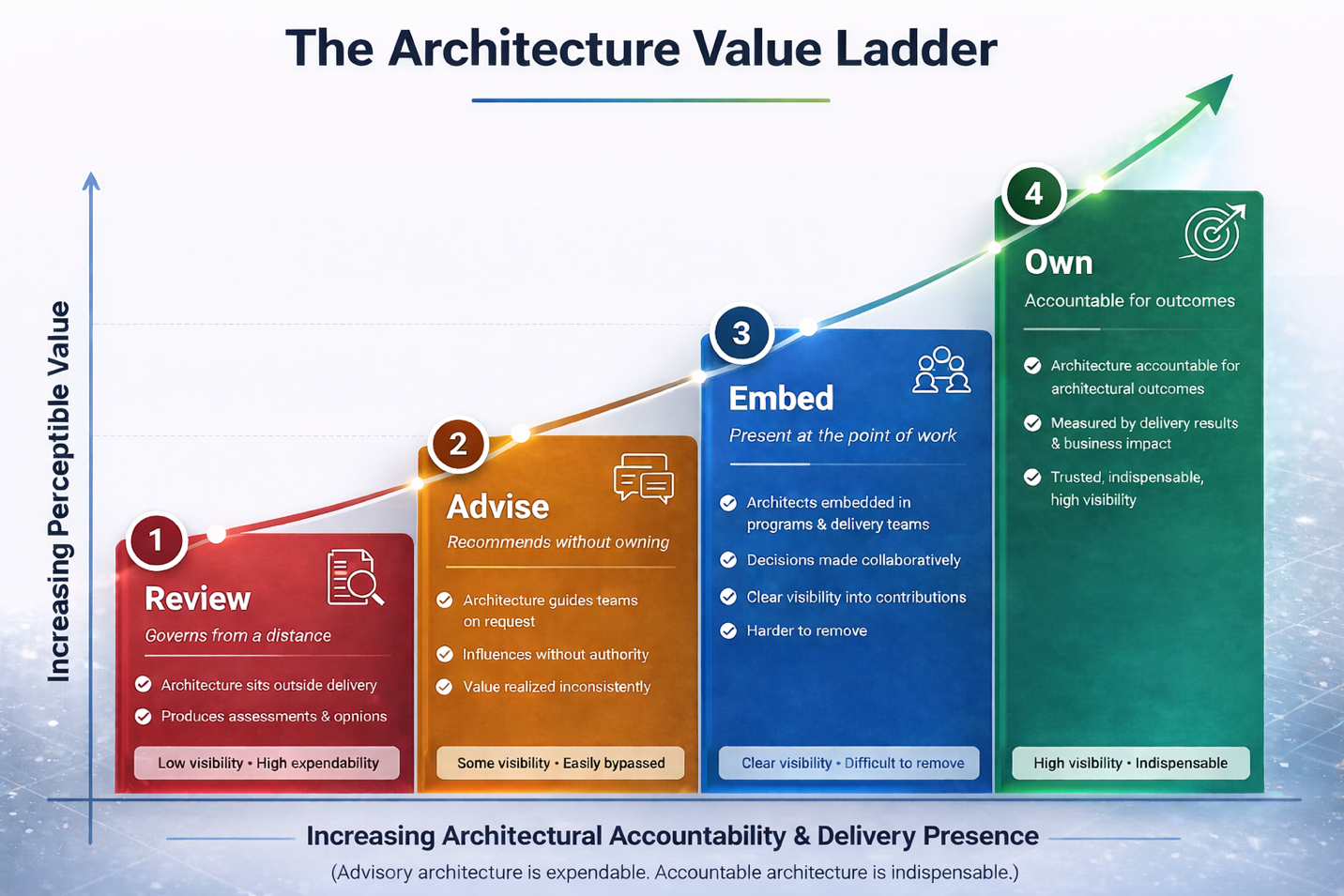
Enterprise architecture organizations face a chronic and self-reinforcing visibility problem. They design, govern, and advise — but they rarely own. The result is a function whose contributions are structurally invisible to the executives who fund it, and whose survival is perpetually contingent on making the case for its own existence. This article argues for a second and complementary path to architectural ownership: taking deliberate control of two of the most operationally consequential assets in the modern enterprise — process automations and the service catalog from which they are accessed and requested. Owning these assets does not just increase architecture’s visibility. It places architecture at the intersection of every automated workflow, every service request, and every operational process that the organization depends on to function — making it indispensable not in theory, but in daily operational practice.
Author: Frank Guerino
The Same Problem, a Different Angle
Architecture organizations that have built a practice around at-risk and high-risk initiatives have solved one dimension of the visibility problem: they are present and accountable when the most consequential delivery work is happening. But crisis-driven engagement, by its nature, is episodic. A program recovers, the practice hands off ownership, and the queue advances to the next engagement. The visibility that crisis work creates is powerful, but it is tied to moments of organizational stress. Between those moments, architecture can still drift back into the background.
Owning enterprise process automations and the service catalog addresses a different dimension of the same problem - one that is continuous rather than episodic. Process automations run every day. The service catalog is consulted every day. If architecture owns and operates these assets, it is not just present at the moment of crisis. It is present at the moment of every automated workflow execution, every service request submission, and every operational dependency that the business has come to rely on. That kind of presence does not require a burning platform. It is structural, persistent, and compounds in value the more the automation estate and service catalog grow.
It is useful, again, to think about the spectrum. At one end is the documentation-heavy architecture function - policies, standards, frameworks, reference architectures. At the other end is the delivery ownership model. Process automations and the service catalog represent a third point on that spectrum worth naming explicitly: operational ownership. Architecture that owns operational assets is not merely present at the point of delivery. It is present at the point of operation - the daily moment when the enterprise depends on its technology to function. That is a fundamentally different and more durable form of organizational relevance.
What Process Automation Means at Enterprise Scale
Process automation at enterprise scale is not a single technology or a single team’s responsibility. It is a landscape of interconnected capabilities that spans the entire organization. Three categories sit at the core of that landscape and represent the primary targets of architectural ownership.
Robotic Process Automation (RPA). RPA automates structured, repetitive human tasks by mimicking the interactions a person would have with a user interface - entering data, navigating screens, copying values between systems, submitting forms. It is typically deployed where no API or direct system integration exists, and where the process is too rule-bound and repetitive to justify ongoing human execution. RPA bots operate across applications, often crossing organizational and system boundaries in the course of a single process, and they are frequently the first automation technology a business unit deploys independently - making them among the most proliferated and least governed components of the enterprise automation estate.
Workflow Automation. Workflow automation manages the routing, sequencing, and tracking of work across people, teams, systems, and time. It governs approval processes, exception handling, task assignment, escalation, notifications, and the conditional logic that determines what happens next at each step of a business process. Workflow automation encodes organizational decision rules and process dependencies directly into executable logic, and it operates continuously as long as the business processes it governs are running. Because workflow automation sits at the intersection of people, systems, and business rules, it is inherently cross-domain and inherently architectural in character - yet it is frequently owned by individual business units or platform teams operating without enterprise design standards.
Orchestration. Orchestration coordinates the execution of multiple automated processes, services, and systems into coherent, end-to-end workflows. Where RPA handles individual task-level automation and workflow automation manages human-facing process routing, orchestration manages the sequencing, dependency resolution, error handling, and state management of complex multi-system, multi-step processes - including integration pipelines, microservice calls, API interactions, data transformations, and downstream trigger events. Orchestration is the highest-order automation capability in the enterprise, and it operates most consequentially at the cross-domain level where architectural oversight is most needed and most often absent.
Beyond these three core categories, the automation estate includes AI-driven automation agents that make decisions and take actions on behalf of human workers, event-driven architectures that trigger downstream processes in response to state changes across the enterprise, and integration pipelines that move and transform data between applications continuously. Any automation that crosses organizational or system boundaries - regardless of the technology through which it is implemented - falls within the scope of what architecture should own and govern.
This landscape is large, growing rapidly, and deeply consequential. In most large enterprises, hundreds or thousands of automated processes run continuously, touching finance, human resources, supply chain, customer service, regulatory reporting, clinical operations, trading, and every other domain that depends on technology to function. When a critical automation fails, business processes stop. When an automation produces incorrect outputs, downstream systems and decisions are corrupted. When automations proliferate without governance, the enterprise accumulates a hidden layer of operational complexity that nobody fully understands and nobody fully owns.
That last sentence describes the state of most enterprise automation estates today. Automations have been built by operations teams, business analysts, platform engineers, IT delivery squads, and individual departments acting independently. They share no common design standards, no consistent metadata, no unified monitoring, and no single point of architectural accountability. They are, collectively, one of the largest and least governed technical assets the enterprise owns - and they sit almost entirely outside the architecture function’s field of view.
Why Architecture Should Own Process Automations
The argument for architecture owning the enterprise automation estate rests on three pillars, each independently compelling and cumulatively decisive.
Architecture already understands the cross-domain dependencies and integration complexity that automation requires. Every meaningful enterprise automation crosses organizational and system boundaries. An invoice processing automation touches ERP, accounts payable, vendor management, and potentially regulatory reporting. A clinical trial data automation touches laboratory information systems, electronic data capture platforms, regulatory submission systems, and data warehouses. A trading reconciliation automation touches order management, settlement infrastructure, risk systems, and compliance reporting. These are not single-system problems. They are integration problems - and integration complexity is precisely the domain where enterprise architecture has the deepest expertise, the broadest enterprise-level visibility, and the greatest ability to make design decisions that hold up at scale. No other function in the enterprise is better positioned to design, govern, and own automations that operate across multiple systems and domains.
Architecture is already designing the processes that automations implement. Enterprise architects define the process models, integration patterns, data flows, and system interaction designs that automation engineers subsequently build against. In most organizations, the architect designs the pattern and hands it off - and then watches as the implementation diverges from the design, accumulates technical debt, and eventually becomes an ungoverned dependency that nobody can fully explain. Taking ownership of the automation that implements the architecture closes that gap. It ensures that the implemented automation reflects the intended design, that deviations are caught and corrected, and that the architecture’s intent is preserved in the operational asset rather than compromised by it. Owning the automation is the natural and logical extension of designing the process it executes.
Automation outputs are architectural artifacts that shape the enterprise’s operational landscape. An enterprise automation is not a transient artifact. It is a long-lived operational system that encodes business rules, integration patterns, data transformation logic, and process dependencies into executable code. Over time, it becomes a load-bearing component of the organization’s operational infrastructure - as consequential as any application, and often far more deeply embedded in daily business operations. Treating automations as peripheral delivery artifacts rather than as architectural assets is a governance failure with operational consequences. Architecture that owns these assets treats them as what they actually are: a layer of the enterprise’s operational architecture that requires the same design discipline, the same lifecycle management, and the same cross-domain coherence as any other architectural domain.
The Service Catalog: Architecture’s Interface with the Enterprise
The service catalog is the organized, governed inventory of services, automations, capabilities, and resources that the enterprise makes available to its users - business and IT alike - for request, consumption, and fulfillment. In a well-designed organization, the service catalog is the front door through which employees request IT services, business units access shared capabilities, partners interact with enterprise platforms, and automated processes invoke downstream services. It is, in short, the interface between what architecture builds and what the enterprise consumes.
Most organizations have something that functions as a service catalog, though it is rarely designed or governed as one. It may be a ServiceNow portal with a list of IT request forms. It may be a confluence page with links to automation runbooks. It may be a collection of APIs documented in a developer portal. It may be all three simultaneously, with no consistent taxonomy, no unified access model, and no clear ownership. The result is a catalog that is simultaneously everywhere and nowhere - fragmented, inconsistently maintained, and practically invisible to the business users who could benefit most from it.
Architecture is the right owner of the service catalog for three distinct and reinforcing reasons.
The catalog is a living inventory of architectural capabilities. Every service in the catalog represents a capability that architecture has designed, governed, or enabled. A service catalog curated by architecture is not merely a list of request forms - it is an organized, navigable, and continuously maintained inventory of what the enterprise’s architectural investments have made possible. When the catalog is owned and maintained by architecture, it becomes a direct and visible expression of architectural value: every capability available to every user in the enterprise, organized by domain, described in business language, and accessible through a governed interface. The catalog makes architectural output tangible in a way that reference architectures and governance frameworks never can.
Owning the catalog puts architecture at the point of every service request. When a business analyst needs a data extract, they go to the catalog. When an operations manager needs a workflow automation, they go to the catalog. When a developer needs an API, they go to the catalog. If architecture owns the catalog, it is present - visibly and operationally - at every one of those moments. It understands what is being requested, by whom, and at what frequency. It can identify patterns of demand that inform future architectural investments. It can surface capabilities that users did not know existed. It can manage access, track consumption, and ensure that the services being requested are the services that the architecture actually supports. That level of operational presence is not achievable through any governance mechanism or standards framework. It requires ownership of the interface itself.
The catalog closes the loop between architectural design and operational consumption. Architecture designs capabilities and services that are intended to meet business needs. Without a governed service catalog, the connection between what architecture designs and what the business actually consumes is indirect at best and invisible at worst. The service catalog is the mechanism through which that connection is made explicit and operational. When architecture owns both the design of a capability and the catalog entry through which it is consumed, it has a direct and continuous feedback loop: it knows whether its services are being used, whether they are meeting demand, whether they need to be updated or retired, and where gaps in the catalog are creating friction for users. That feedback loop makes architecture more responsive, more relevant, and more tightly integrated into the daily operational rhythm of the enterprise.
What Ownership Actually Means
Claiming ownership of enterprise process automations and the service catalog is not a passive assertion. It requires architecture to take on genuine operational responsibilities that go beyond design and governance. Specifically, it means:
-
Maintaining a complete and authoritative inventory of all enterprise automations, organized by domain, technology, business process, and operational dependency
-
Establishing and enforcing design standards for automation development across all three primary automation categories - Robotic Process Automation (RPA), Workflow automation, and Orchestration - as well as integration pipelines and AI agents, so that all automations across all technologies are consistently designed, documented, and maintainable
-
Owning the lifecycle of automations from initial design through implementation, operational monitoring, change management, and retirement
-
Owning the service catalog end to end: taxonomy, content, access governance, fulfillment workflows, and the operational processes that ensure catalog entries remain accurate, discoverable, and aligned with what the architecture actually supports
-
Monitoring automation health and service catalog consumption continuously, with metrics reported to IT and business leadership as a regular operational artifact
-
Acting as the integration point between automation platforms, service management systems, and the broader architectural landscape - ensuring that automations and catalog services are coherent with each other and with the systems they connect
This is not a small scope. It is a genuine operational domain with real accountability, real users, and real consequences when things go wrong. That is precisely the point. Architecture that accepts this scope has moved from advisory to operational - and operational ownership at this scale creates exactly the kind of daily, structural, compounding visibility that cannot be achieved through governance alone.
The Compounding Effect
The automation estate and the service catalog are not static. They grow. Every new automation added to the estate is another operational asset that architecture owns, governs, and is accountable for. Every new service added to the catalog is another point of contact between architecture and the users who depend on it. As the estate and the catalog grow, architecture’s operational footprint in the enterprise grows with them - automatically, structurally, and without requiring a new executive mandate or a new organizational charter.
This compounding effect has a second dimension that is equally important: intelligence. An architecture function that owns the automation estate and the service catalog accumulates, over time, an unparalleled view of how the enterprise actually operates. It knows which processes are automated and which are still manual. It knows which services are heavily consumed and which are underutilized. It knows where automation failures are creating operational disruptions. It knows where demand for catalog services is outpacing current supply. That operational intelligence is not just a byproduct of ownership - it is a strategic asset that makes every other architectural activity more informed, more targeted, and more credible.
C-level leaders who might once have questioned whether architecture was doing anything important will find a different answer when architecture owns the systems that run the enterprise’s daily operations, maintains the catalog through which every team accesses enterprise capabilities, and can speak with authority about the operational health of the automation estate and the consumption patterns of the service catalog. That is not an advisory function. That is an operational one. And operational functions are not expendable.
The Spectrum, Revisited
This article, like its companion piece on at-risk and high-risk initiatives, is ultimately about moving architecture along a spectrum: from documentation-heavy and advisory at one end, toward accountable ownership at the other. The at-risk initiative practice moves architecture toward ownership at the moments of greatest organizational stress. Owning process automations and the service catalog moves architecture toward ownership in the fabric of daily operations.
These are not competing strategies. They are complementary ones. An architecture organization that runs an at-risk initiative practice and owns the enterprise automation estate and service catalog has achieved something that most architecture organizations never reach: it is present and accountable at both ends of the delivery and operational cycle. It is in the room when things break, and it is in the room - every day - when things run. That dual presence is what transforms architecture from a function that justifies its existence to a function whose absence would be immediately and concretely felt.
The documentation still matters. Standards still matter. Reference architectures still matter. But none of those outputs, however carefully crafted, can substitute for the organizational relevance that comes from owning something the enterprise depends on. Process automations and the service catalog are exactly that kind of asset - consequential, growing, and entirely consistent with the architectural expertise that the function already possesses. The case for architecture owning them is not just strategic. It is obvious.
A Real-World Example: The Power of Automation Ownership in Life Sciences
The case for architecture owning enterprise process automations and the service catalog is not purely theoretical. At a major global life sciences and pharmaceutical company, a compelling example of what automation ownership can accomplish - and of the additional value that could be unlocked by anchoring that ownership within the architecture function - played out over several years in one of the most operationally critical areas of the business: manufacturing. The enterprise architecture organization at this company is, by any fair measure, a mature and visible function with significant organizational credibility. The example that follows is not a story of architectural failure. It is a story of demonstrated automation value and of an opportunity to amplify that value further by connecting it more explicitly to the architectural function already doing cross-domain work across the enterprise.
The starting point was a problem familiar to anyone who has managed complex technical infrastructure in a regulated manufacturing environment. Provisioning the computing assets required to support manufacturing operations - virtual infrastructure, validated environments, domain-specific configurations - was an entirely manual process. Teams of specialists with deep domain knowledge handled each provisioning request by hand. The work was intricate, the validation requirements were exacting, and the consequence of error in a GxP-regulated manufacturing environment was not merely a support ticket but a potential compliance failure. The result was delivery timelines that stretched from six to nine months for assets that were, in many cases, structurally identical to assets that had been delivered dozens of times before. Throughput was constrained by headcount: only a limited number of people had the specialized knowledge to perform the work, which meant that the quantity of assets that could be delivered in any given period was capped by the size of a small and difficult-to-scale team. Human error introduced additional risk to every delivery, regardless of the care taken.
An ancillary non-architecture IT group identified this as a prime candidate for automation and took ownership of the problem. What followed was one of the most compelling demonstrations of automation value in the enterprise. The team automated not just the provisioning process itself, but significant portions of the testing and verification workflow - including the Installation Qualification and Operational Qualification processes that regulated manufacturing environments require before assets can be placed into production use. IQ/OQ is typically among the most time-consuming and resource-intensive aspects of manufacturing IT delivery, requiring documented evidence that every system component has been installed correctly and operates as intended within its validated environment. Automating these processes was not a minor efficiency gain. It was a transformation of the delivery model.
The results were dramatic and measurable. Delivery timelines that had taken six to nine months collapsed to hours or days for standard asset configurations. Quality improved significantly - automated provisioning and verification eliminated the class of errors that human execution inevitably introduces, producing more consistent and more reliably validated outputs than the manual process had been able to achieve. The team went further, developing repeatable automation frameworks that allowed domain-specific IQ/OQ processes to be designed, built, and deployed far more quickly for new asset types - effectively creating a reusable pattern library for manufacturing IT delivery that compressed future automation development cycles substantially.
The team also built a modern, purpose-designed self-service catalog that allowed stakeholders to configure desired assets, select from validated templates, and initiate on-demand provisioning without requiring manual intervention at every step. This catalog was a direct expression of the automation work: the assets available in it were the assets the team had automated, described in the language of the people who needed them, configurable to the parameters those users actually cared about, and backed by the automated delivery and verification processes that made rapid, high-quality fulfillment possible. By any operational measure - speed, quality, consistency, user experience - this purpose-built catalog outperformed the broader enterprise service catalog, which continued to offer a more limited set of IT services through fragmented delivery organizations that fulfilled requests with considerable inconsistency in both timeline and quality.
In a span of just a few years, the automation organization had saved the enterprise a quantifiable and substantial amount of time and money, had transformed a constrained and error-prone manual process into a scalable and reliable automated one, and had built operational credibility that extended well beyond its original manufacturing scope. It had become a critical IT organization - not because anyone had granted it that status, but because the business depended on it and knew it.
And throughout this period, a recurring question surfaced from stakeholders across different parts of the organization: why was this team not part of the enterprise architecture organization? The question was offered as a compliment to both the automation team and to architecture - a recognition that the work the automation team was doing sat naturally alongside the cross-domain, process-oriented, integration-aware work that architecture performs across the enterprise. Vertical process automation touches the same integration patterns, the same cross-domain dependencies, and the same enterprise coherence concerns that architecture already manages. The observation was not that architecture had dropped the ball. It was that the automation team had built something so architecturally aligned in character that the organizational case for bringing it formally under architecture’s umbrella was increasingly self-evident. The automation team had earned its own strong organizational standing - and the recognition that its work belonged within architecture was a testament to that success, not a criticism of where it had started.
The lesson this example offers is clear and encouraging. Automation ownership at enterprise scale produces results that manual processes and advisory governance simply cannot match: the speed, quality, and scalability gains are not incremental but transformational. The enterprise architecture organization at this company is already a visible and credible function - precisely the kind of organization that is well positioned to extend its influence by formally taking on ownership of assets like the automation estate and the service catalog. Where architecture has already earned strong organizational standing, adding operational ownership of automation and catalog assets does not create credibility from scratch - it compounds the credibility that already exists, connecting the architecture function’s enterprise-wide perspective to the operational layer where cross-domain automation work naturally lives. The opportunity this experience points toward is one of amplification: taking work that has already proven its value and giving it the architectural home, the governance framework, and the cross-organizational reach that would make it even more impactful.
Taking on ownership of the enterprise automation estate and service catalog requires a specific staffing orientation that differs somewhat from the delivery-crisis profile described in the at-risk initiative practice. The architects who own these assets need deep delivery experience, but they also need a strong operational orientation - an ability to manage running systems, govern living catalogs, and sustain continuous accountability rather than sprint-based engagement models.
Automation architects with cross-domain integration depth. The architects responsible for the automation estate should have hands-on experience with the three primary automation categories - Robotic Process Automation, Workflow automation, and Orchestration - as well as with integration platforms and AI agent frameworks. They need the cross-domain integration knowledge to understand how automations interact across the systems and organizational boundaries they connect, and the design discipline to govern a diverse automation estate with consistency and coherence.
Service catalog architects with business and operational fluency. The architects responsible for the service catalog need a different profile: strong business communication skills, a clear understanding of how different user communities - business analysts, operations managers, IT developers, executives - interact with enterprise capabilities, and the organizational credibility to work with domain leaders across the enterprise to ensure that catalog content is accurate, comprehensive, and aligned with how the business actually wants to consume architectural services. This is as much a communication and relationship role as it is a technical one.
A governance and operational discipline. Both sets of architects need to operate with the discipline of a managed service function: consistent processes, regular reporting cadences, defined service levels, and proactive communication with stakeholders when the assets they own are at risk or underperforming. This is not the episodic, crisis-driven engagement model of the at-risk initiative practice. It is a continuous operational responsibility, and it should be staffed and managed accordingly.
Standing the Practice Up
Taking ownership of the automation estate and service catalog does not require starting from scratch or claiming everything at once. The most effective path is an incremental one, beginning with the assets that are closest to architecture’s existing work and expanding from there.
Start with an inventory. Before architecture can own the automation estate, it needs to know what exists. A focused discovery exercise - working with IT operations, platform teams, and business units - will surface the scope of the existing automation landscape: what is running, who built it, what it connects, and what governance exists today. The same exercise applied to existing service catalog assets will reveal what is already cataloged, what is missing, and where the most significant gaps between architectural capability and catalog accessibility lie.
Establish a governance model early. The architecture organization should define, publish, and begin enforcing design standards for new automations before it attempts to remediate the existing estate. This creates a clear line of ownership going forward and builds the governance muscle that will eventually be applied retrospectively. The same approach applies to the service catalog: define the taxonomy, the entry standards, and the ownership model for new catalog additions, and use that framework as the basis for rationalizing what already exists.
Make the catalog visible and useful immediately. One of the fastest ways to demonstrate the value of architecture owning the service catalog is to make it dramatically better than it was before architecture took it over. A well-organized, clearly described, business-language catalog that actually reflects what the enterprise can do - versus what it used to do, or what a vendor template suggested it might do - creates immediate operational value for users and immediate credibility for architecture with the business leaders those users report to.
Report consumption and automation health as operational metrics. From the first month of ownership, architecture should be producing and sharing operational reports: how many services are in the catalog, how many requests are being fulfilled, which automations are running and at what health levels, where demand is concentrated, and where gaps are creating friction. These metrics are not just governance artifacts - they are the evidence that architecture is doing something operationally consequential, and they should be in front of IT and business leadership on a regular cadence.
Closing Thought
Architecture’s visibility problem is not solved by producing better documentation. It is not fully solved by crisis-driven delivery engagement, however important and effective that model is. It is solved, ultimately, by owning assets that the enterprise depends on - assets that run every day, that users interact with every day, and whose absence or failure would be immediately and concretely felt by the people who run the business.
Enterprise process automations and the service catalog are exactly those assets. They are consequential, growing, and structurally aligned with the expertise that architecture already possesses. Owning them does not require architecture to become something it is not. It requires architecture to extend what it already does - designing cross-domain processes, governing integration complexity, and managing the enterprise’s technical capabilities - into the operational domain where those designs actually run.
The architecture organization that owns its automation estate and its service catalog does not need to explain its value to the CIO. The CIO already knows. Every business unit leader who submits a service request, every operations team that depends on an automation running cleanly, and every executive who reviews the operational metrics that architecture produces already knows. That is what operational ownership delivers. And it is available to any architecture organization willing to claim it.
Published by Guerino Enterprises, LLC – Copyright Guerino Enterprises & Frank Guerino